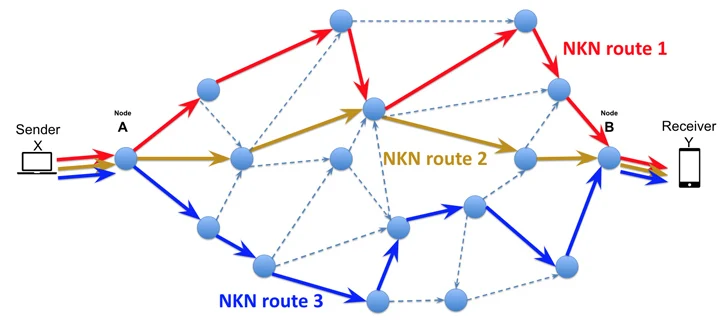
A newly identified cyber threat named NKAbuse is making waves in the digital security landscape, employing a decentralized, peer-to-peer network protocol called NKN (New Kind of Network) as a conduit for its malicious activities.
Russian cybersecurity firm Kaspersky disclosed in a recent report that the malware harnesses NKN technology for seamless data exchange between peers, acting as a robust implant with both flooder and backdoor functionalities.
NKN, boasting a network of over 62,000 nodes, stands as a revolutionary software overlay network built upon the existing Internet infrastructure. It allows users to share unused bandwidth and earn token rewards, incorporating a blockchain layer atop the TCP/IP stack.
In a departure from typical threat actor tactics, NKAbuse leverages blockchain technology not only for command-and-control communication but also to execute distributed denial-of-service (DDoS) attacks, operating as an embedded implant within compromised systems.
The malware, coded in the Go programming language, exhibits a preference for targeting Linux systems, including Internet of Things (IoT) devices. While the full extent of the attacks remains uncertain, Kaspersky highlighted a specific incident involving the exploitation of a six-year-old critical security vulnerability in Apache Struts (CVE-2017-5638, CVSS score: 10.0) to infiltrate an undisclosed financial institution.
Upon successful exploitation, NKAbuse deploys an initial shell script responsible for retrieving the implant from a remote server, contingent on the verification of the target host’s operating system. The malware accommodates eight distinct versions tailored to various CPU architectures, reinforcing its adaptability.
Unlike some malware counterparts, NKAbuse lacks a self-propagation mechanism, necessitating delivery through an alternative access pathway, such as the exploitation of existing security vulnerabilities.
Surviving system reboots is achieved through the utilization of cron jobs, requiring root access. The malware, upon confirming a user ID of 0, integrates itself into the system’s crontab, ensuring persistence after each reboot.
Noteworthy features of NKAbuse include a comprehensive array of backdoor capabilities. These include sending periodic heartbeat messages to the bot master, transmitting system information, capturing screenshots, executing file operations, and running system commands.
Kaspersky emphasized the meticulous design of NKAbuse, tailored for integration into a botnet while maintaining flexibility as a standalone backdoor. The incorporation of blockchain technology ensures both reliability and anonymity, hinting at the potential for the botnet’s gradual expansion without a discernible central controller.
Found this news interesting? Follow us on Twitter and Telegram to read more exclusive content we post.